TL;DR:
- Inventory your user accounts and remove unused ones
- Change weak and reused passwords
- Enable 2FA and make sure you configure backup options
Once in a while you should assess the security of your user accounts. For various reasons your protection might not be optimal anymore.
Whenever one of your online accounts gets compromised it's important to change your password as soon as your learn about the data breach. Make sure to monitor your data breach exposure to discover these events as soon as possible. Also enable multi-factor authentication for the breached account if you haven't done so yet.
But in this article I want to focus on the improvements that are less urgent, but nevertheless important to address on a regular basis. The good thing is, you don't have to do everything at once. But when you have some time to kill, just improve the security of a few of your accounts with these tips.
Inventory your user accounts
Do you still know all the accounts you ever created? Probably not. Unless you've consistently written them down, or saved them all in a password manager.
If you don't have a good overview of your user accounts I really encourage you to put some effort into it. Good security starts with knowing your assets. Every online account, and certainly abandoned ones, add up to your overall data exposure risk.
I think I covered most of my accounts. When I started using a password manager I added all the accounts I knew I had. Additionally I searched all my mailboxes for password reset or registration mails and I found a lot of accounts I already had forgotten about.

Remove unused accounts
Once you have compiled the list of your user accounts, it's time to remove the unused ones. One of the basic principles of good security is to reduce your attack surface. What you don't have cannot be stolen. Unfortunately not all online services foresee the option to delete your account.
When this feature is lacking, ask the company to remove your account. GDPR enables people living in the European Economic Area to exercise "the right to be forgotten".
Change weak and reused passwords
Even if you're not aware that an online service you're registered for suffered a data breach, change the password if it's a weak or a reused one. Some browsers provide (built in) options to track insecure passwords or you could for instance use Okta's PassProtect browser plugin. For more detail, see this post.

Enable multi-factor authentication where possible
If a website offers multi-factor authentication (MFA) activate it. Yes even if it's SMS based 2FA. Unfortunately we depend on which form of 2FA a particular website offers.
If you want to know which sites offer 2FA you can use 2FA Notifier, a handy plugin available for Chrome and Firefox. The plugin compares the website you are visiting to a list of known 2FA capable websites provided by twofactorauth.org
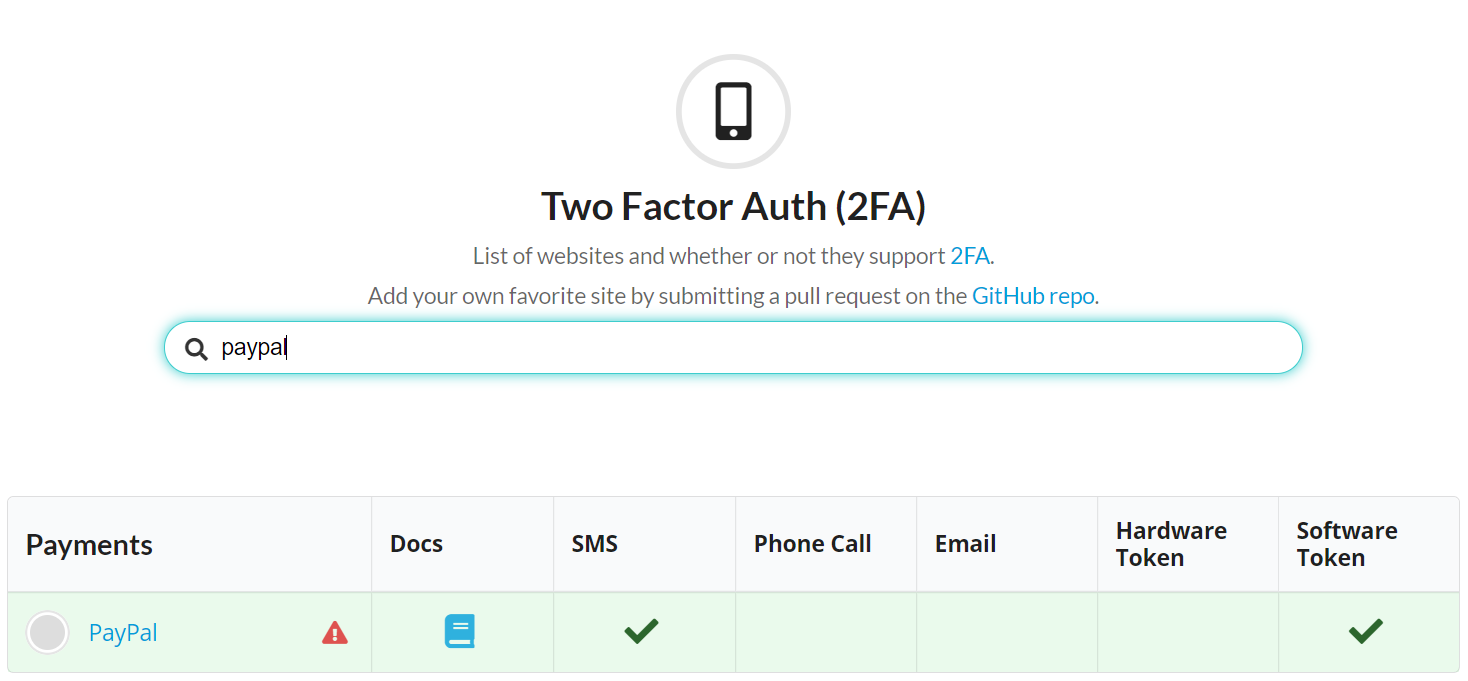
Consult this website once in a while to see if websites you use offer an improved implementation of 2FA.
Configure MFA backup options
If you have enabled MFA make sure that you have configured backup option(s). If you can't provide the verification code, for whatever reason, you still need to be able to access your account.
A lot of sites offer 2FA backup codes for instances. Copy them and store them securely. Or when a service offers multiple implementations of 2FA, consider activating at least two.
Some sites offer only one form of 2FA, for instance via authenticator app. That's why it's important that the authenticator app you use also has backup options. This is often overlooked. I learned this the hard way myself!
Regularly review your online account's #security settings! Just changed my authenticator app to Authy on a site where I still used Google authenticator. Reason? With Authy you can easily recover access when phone dies or is stolen. Trust me, I learned it the hard way 😆#Infosec
— John Opdenakker (@j_opdenakker) June 9, 2019
Use email aliases
Most online services use email address as login. Consider changing the email address(es) you use for your different accounts into a specific alias for each account. This has a few advantages:
- It can be used as part of defense against credential stuffing attacks
- It can help to detect the source of a data breach
- It can help to track how your data are shared or sold with other services.
Final note
Keeping your accounts as secure as possible is an ongoing exercise. Evaluate your passwords and 2FA configurations on a regular basis. As we have seen there are tools to help you, use them to your benefit. Applying these best practices will give you as much control as possible and will make you feel at ease when a data breach happens.




