I love good security quotes, aphorisms and statements because they often hold a lot of truth and wisdom. That's why I decided to bundle the ones I like in a blog. I can't attribute several of them at the moment, if you know from who they originally are, please let me know. If you have other good quotes feel free to leave a reply or reach out on Twitter.
Data breaches
Everytime companies have a data breach you can almost predict what will be in the disclosure notice.
We take your security seriously.
Or even worse...
We take your security extremely seriously.
And since GDPR and other data privacy regulations are applicable a lot of companies use statements like this:
We have members' privacy at the heart of everything we do.
Well, obviously they didn't take our security and privacy seriously enough. That's why this kind of statements really piss me off.
The next quote by Dmitri Alperovitch is an unfortunate truth:
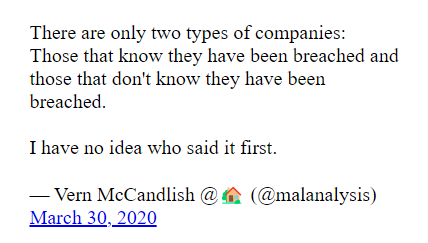
Another one that's very applicable to data breaches:
Still a lot of companies don't own when they are hacked or suffer a data breach, but instead try to downplay the incidents and blame others.
A breach alone is not a disaster, but mishandling it is. – Serene Davis
It's often hard for security professionals to get security budget, but keep in mind that a data breach will cost a company a lot more than the preventive measure.
If you can't afford security, you can't afford a breach.
— phr00ts (@phr00ts) March 30, 2020
The life of an information security professional
Unfortunately all the (preventive) work infosec professionals do is not always visible or appreciated.
"Rarely is anyone thanked for the work they did to prevent the disaster that didn't happen."
– Mikko Hypponen
And another great one from Mikko:
"Working in information security is sometimes a bit like playing Tetris: your successes disappear but your failures accumulate".
IoT
I think the next quote is brilliant.
The S in IoT stands for security.
However things are improving a bit, it's well known that a lot of IoT devices are inherently insecure or as Mikko Hypponen states:
If it’s Smart, it’s Vulnerable.
— @mikko (@mikko) March 31, 2020
Hypponen's law
Hacking and online crime
Social engineering and phishing in particular is the most used and most succesful attack vector.
"Amateurs hack systems, professionals hack people". – Bruce Schneier
Attackers have a big advantage over defenders:
"Hackers only need to be lucky once. You need to be lucky every time."
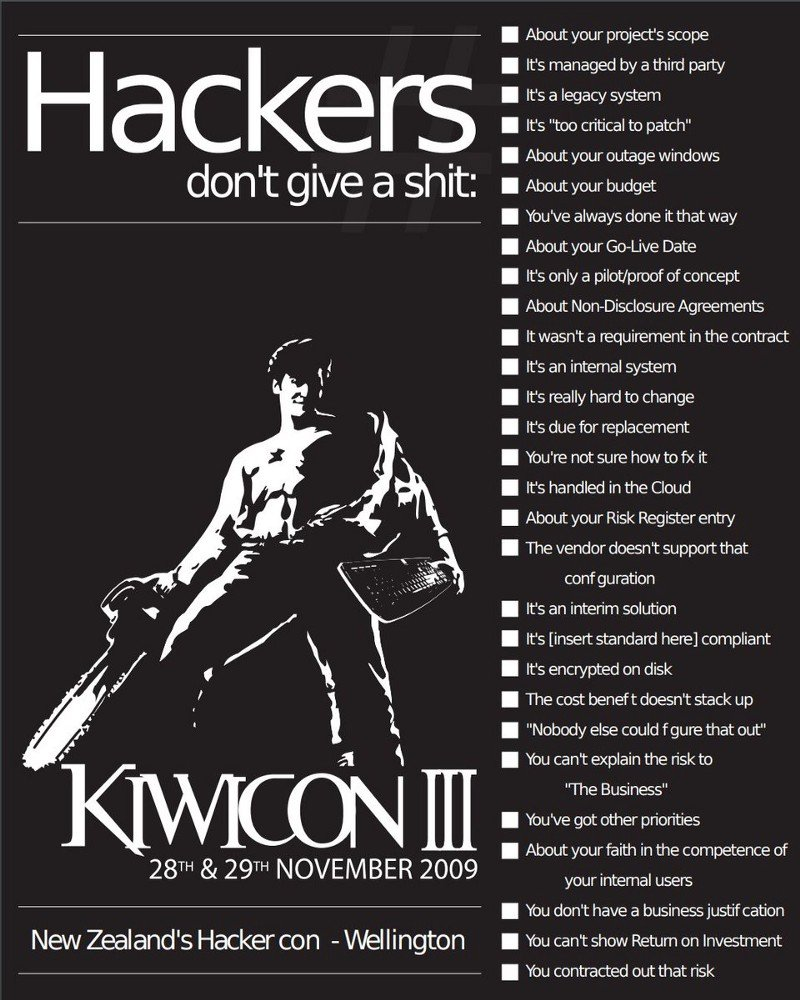
Criminals don't care about all your possible excuses:
Criminals don’t give a fuck that you’re not able to patch your software on time
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) January 14, 2020
Criminals don’t give a fuck that you always did it like this
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) March 29, 2020
Criminals don’t give a fuck that you always did it like this
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) March 29, 2020
Criminals don't give a fuck that you don't have enough security budget
— John Opdenakker - Lockdown counter: 32 (@j_opdenakker) April 9, 2020
These tweets are inspired on this brilliant poster from the KiwiCon hacker conference.
Cyber crime has evolved:
"Today the hackers we see are not just graffiti artists, they are organized criminals." – Mikko Hypponen
But this doesn't mean that all attacks are advanced ones. Hacking data out of a system can be as easy as incrementing a number in a url.
If you can count you can hack
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) February 21, 2020
- IDOR
IDOR stands for Insecure Direct Object Reference
And like Mike Thompson said at Bsides London, nothing is unhackable!
You're missing two classics!
— Mike Thompson (@AppSecBloke) May 14, 2020
"If you think your product is unhackable, just think it. Never say it" - @AppSecBloke on companies claiming their stuff can't be hacked
"If you can count, you can hack" @j_opdenakker on enumeration attacks using things like IDOR
Zero days
There's often a lot of fuzz about zero days, but in reality attackers are far more likely to exploit the humans, for instance via phishing attacks.
Give a man an 0day and he'll have access for a day, teach a man to phish and he'll have access for life.
— thaddeus e. grugq (@thegrugq) February 7, 2015
Via emails...
Who needs zero-days when there’s email
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) January 27, 2020
that can contain attachments with malicious macro's
Who needs zero-days when there are Excel Macros https://t.co/xu8ea58yKv
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) February 6, 2020
Or they can just get access to the internal network via poorly secured servers.
Who needs zero days when you can brute force RDP#Infosec pic.twitter.com/nHHKU2M0gB
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) March 2, 2020
Computer viruses
"The problem of viruses is temporary and will be solved in two years”. – John Mcafee, 1988
Compliance vs. Security
Compliance can be helpful to improve the security in an organization, but...
"Compliance is not security."
Also:
Criminals don’t give a fuck if you’re ISO 27001 compliant
— John Opdenakker (@j_opdenakker) December 10, 2019
Or the more polite version, in a nice tile!
Quote by @j_opdenakker#infosec #infosecquoteoftheday pic.twitter.com/DwFcHHsBsl
— Rens (@mosymuis) July 9, 2020
Encryption
"Dance like nobody is watching, encrypt like everyone is".

Encryption requires proper key management, and this is often not easy...
“You start with a data privacy problem, and cryptography replaces it with a key management problem.”
And please...
"Don't roll your own crypto."
Backups
Backups can help you get your data back in case of computer (hard disk) crashes or when you become victim of a ransomware attack. But if you don't test to restore them regularly you may have some unpleasant surprises when you really need them.

HTTPS
HTTPS & SSL doesn't mean "trust this." It means "this is private." You may be having a private conversation with Satan.
– Scott Hanselman
The Internet
"The internet is a garden of low-hanging fruit." – Mikko Hypponen
“Trying to delete your data from the internet is like trying to take piss out of a pool.” – Troy Hunt
"Gmail has become the single sign on system for the whole internet." – Mikko Hypponen
Privacy
There are a lot of "free" (online) services. But keep in mind there's no such thing as a free lunch...
"If you’re not paying for the product you are the product."
And unfortunately it's really hard to preserve a bit of your privacy:
"Privacy is not for the passive." – Jeffrey Rosen
Users
Some of the next quotes might be a bit controversial or sound harsh. Let me first and for all make clear that I think user blaming is not the way to go. But it's also a fact that there's still a lot of work to do when it comes to user awareness and education.
"The user's going to pick dancing pigs over security every time." – Bruce Schneier
If a human can make it, a human can break it.
— O³BTW which one’s Pink? (@0x0zone) January 7, 2020
"I am regularly asked what the average Internet user can do to ensure his security. My first answer is usually 'Nothing; you're screwed'." – Bruce Schneier
Here's one more infosec law: the law of an end user
— Adam (@Hexacorn) April 9, 2019
𝘛𝘩𝘦 𝘦𝘯𝘥 𝘶𝘴𝘦𝘳 𝘪𝘴 𝘯𝘰𝘵 𝘢 𝘴𝘦𝘤𝘶𝘳𝘪𝘵𝘺 𝘤𝘰𝘯𝘵𝘳𝘰𝘭.
But as an end user you can certainly take some actions to improve your security.
Lock your computer: "Control + Alt + Delete when you leave your seat."
And be careful for phishing and other scams: "If you suspect deceit, hit delete!"
These last 2 quotes and more good ones about user awareness can be found on this website, although I don't agree that passwords are like underwear.
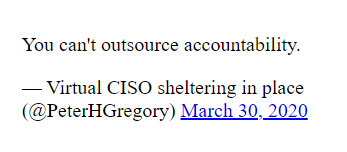
Trust
"Trust is not a security control."
Or at least not a very good one. That's why you should...
"Trust but verify."

Technology trust is a good thing, but control is a better one. — Stephane Nappo
Security Awareness
You can only improve security when you realize you’re at risk.
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) February 3, 2020
"Just because you can, doesn't mean you should."
One of the biggest security risks is denying that you’re at risk.
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) March 17, 2020
A lot of companies and people don't have an overview of their assets, which puts them in a very vulnerable position.
Securing your assets starts by knowing them.#Infosec
— John Opdenakker - Lockdown counter: 12 (@j_opdenakker) March 21, 2020
And it's not because you don't know that you're hacked that you're not hacked:
"Absence of evidence is not evidence of absence."
And trusting on good reputation of a company doesn't give any guarantees either...
"Reputation is a very poor security control." – Troy Hunt
It's often hard to change the habits of people...
"We have always done it like this."

Keep in mind that (the need for) security never stops:
"Security is a journey, not a destination."
And that security can't be solved by technology only...
"If you think technology can solve your security problems, then you don't understand the problems and you don't understand the technology." -Bruce Schneier
Security controls
This one doesn't need any explanation.
“Relying on [one technical control] is like erecting a pole in your front yard and hoping your adversary runs into it.” -Bruce Schneier https://t.co/gdxmAz0d9f
— ch3f (@damonsmall) March 30, 2020
Security controls should be as frictionless as possible. If security measures make applications and processes hard to use, users will try to bypass them.
The secret of good security controls is that they don’t feel like security controls.
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) January 20, 2020
Secure development
"A good programmer is someone who always looks both ways before crossing a one-way street." – Doug Linder
Security absolutism
Security absolutism is unhealthy. There's no such thing like 100% secure. But...
"Don't let perfect be the enemy of good." – (variation on aphorism by) Voltaire
Sometimes we just have to deal with the options that are available. One of the examples is SMS 2FA.
Sms based 2fa is better than no 2fa
— John Opdenakker - Lockdown counter: 12 (@j_opdenakker) January 13, 2020
Defense in Depth
Attackers will try to find a way to break into your systems and they will exploit the weakest link. That's why it's important to implement a layered security approach.
"A chain is only as strong as its weakest link".
"Security in IT is like locking your house or car – it doesn’t stop the bad guys, but if it’s good enough they may move on to an easier target". – Paul Herbka
It's always DNS
It's kind of a running gag, when some big service providers have downtime for instance: "It's always DNS."
Except when it's an expired TLS certificate of course.
It's always DNS, except when it's an expired cert
— John Opdenakker - Lockdown counter: 11 (@j_opdenakker) February 3, 2020
Got more good security quotes, let me know!