With the blogs in this series I want to reach not only my typical audience, security professionals, but especially less security aware people to help them improve their personal security. If you think the content is helpful for people you know, share it with them!
Yesterday I wrote about ransomware. What it is, how you can protect yourself in the best possible way and what you can do if you become victim.
Today's post is about phishing, another massive online threat. And just like ransomware phishing will be a plague for many more years to come.
Phishing is a form of fraud in which people are contacted by email, telephone or text message by criminals. They pose as a legitimate entity or person to lure their targets into providing personal information such as banking and credit card details or username and passwords.
Anti-phishing best practices
- Never disclose sensitive information such as passwords or credit card data over the phone, via email or text.
- Never click links in emails or text messages that you received from an unknown sender.
- It's best that you don't click links at all, even if you think it might be a legitimate email or it comes from a known sender. It's always safer to browse to the website directly than to click a link.*
- Enable multi-factor authentication. It is an additional barrier for the attackers to gain access to your accounts. If you don't know what multi-factor authentication is and how to configure it read this and this article.
*Even if an email comes from a known sender this doesn't mean that it can't be a phishing mail. The sender's email account can be hacked, or the attackers can fake the email address of the sender.
We will see that it's not always easy to discover phishing attempts. That's why respecting these general rules is so important. It's much safer to be too cautious than reckless. Your personal data is at stake.
How to recognize phishing phone calls, emails and text messages
An example of phishing via telephone would be if you get a call from a criminal that pretends to be an employee of your bank and asks your credit card info or banking credentials.
Criminals can apply caller ID spoofing, a service that allows them to masquerade as the bank employee by falsifying the number that appears on your caller ID display. So even if the phone number seems the correct one it might not be your bank calling. Like we saw earlier, as a general security practice, you should never provide any sensitive personal data to anyone over phone, via email or text message.

Phishing emails and text messages have some characteristics that can help you to discover them. Here's an example of a PayPal phishing email.
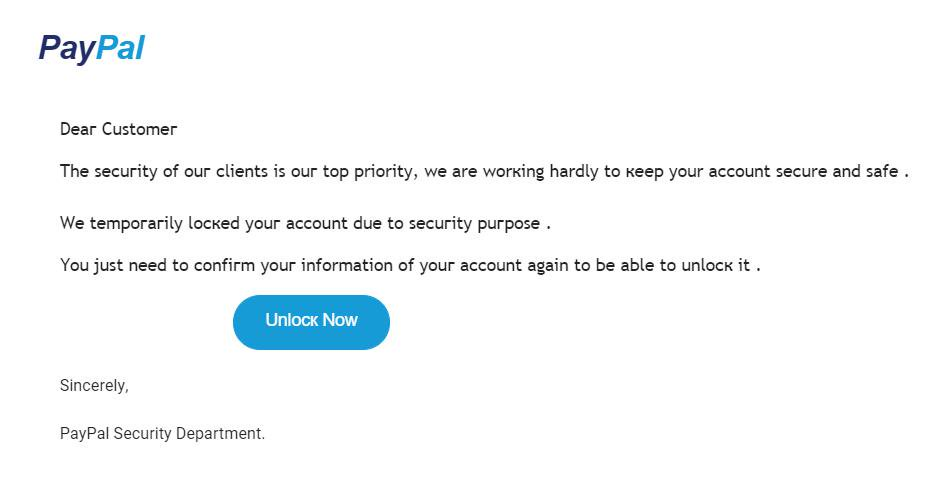
There are a few red flags in this email:
- The Security Department of PayPal will not email you. Like often with phishing this email is unexpected.
- Also notice that the letter "k" looks really strange, there's something weird with this font.
- All 3 sentences have a space before the period at the end of the line.
- Other grammatical errors like "we are working hardly to keep your account secure and safe". PayPal would never say that, right ;)?
Other indicators of phishing that you don't see in this screenshot:
- When I hovered over the "Unlock Now" button i saw a dodgy URL which didn't refer to the official paypal.com domain.
- The sender email address was also suspicious and not from the expected "@mail.paypal.com" domain.
Note that on mobile devices there is no mouse-over or preview functionality so you can not preview the link, hence why it's better to not click any links but browse directly to website instead.
Criminals also often use urgency or fear to convince people. If you see messages like the one below you can be quite sure it's phishing.
"If you don't login to your PayPal account within 24 hours will be no longer able to access your account."

Phishing via email doesn't always imply clicking a link that leads to a malicious website. There's also this type of mails that want to trick you in handing over a lot of personal data to claim your price of 5 million dollar(!!!).
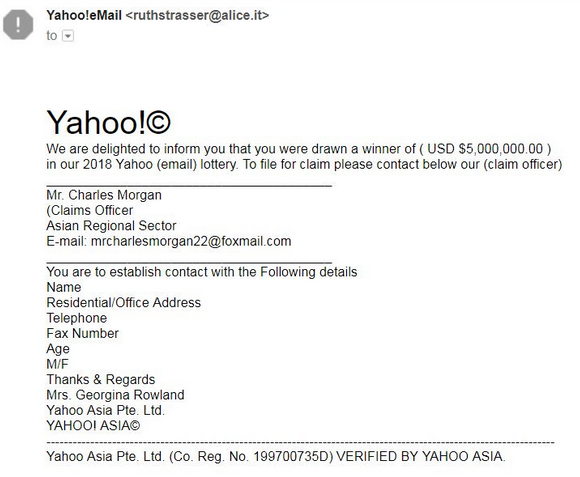
Don't fall for this, you cannot win a prize from a lottery in which you did not participate. Remember, if it's too good to be true, it's just not true.
How to recognize phishing websites
The time that phishing sites where really poorly designed and only available over HTTP are long gone. HTTPS is becoming the rule for phishing sites, and it's becoming more and more difficult to visually distinguish a phishing site from the legitimate site.
The best way to recognize a phishing site is by inspecting the URL. If the URL doesn't match with the URL of the official website you know it's a malicous site. That's why criminals create URLs like this.
www.paypa1.com
or
www.paypal.com.evil.hacker
If you use a password manager it can help you to detect phishing sites. Many password managers will suggest to automatically fill username and password fields at account login. But they do so only if the URL of the visited site matches with the URL you have stored. Your password manager won't suggests to autofill your username and password for paypal.com on the paypa1.com website.
These examples that I gave might seem quite easy to detect, but criminals are a lot more creative than me. On a mobile device this can be a lot harder to detect though. Certainly the second one. The screen size is small and people might only see www.paypal.com instead of the full url www.paypayl.com.evil.hacker and conclude the site is legitimate.
Be aware of events that trigger phishing attacks
There are some events that increase the likelihood of phishing attacks. To name a few:
- After a major incident, for instance a natural disaster like hurrican Harvey in 2017.
- Before major events like the Olympic Games or pop concerts. There's a lot of interest in these events and there's often scarcity of tickets.
- During certain recurring events, like the yearly tax declaration season.
- In the aftermath of a data breach. Criminals send fake password reset links and instead of your password being reset they capture it to gain access to your account.

Phishing is all about exploiting human emotions. Criminals very well know that people are much more susceptible for phishing attacks when certain events happens.
Train yourself
If you want to improve your phishing detection skills in a safe environment, you can do some phishing tests for instance here or here.
What if you've been phished?
If you suspect you fell for a phishing attack it's important to immediately change your password. Here you can read how you can create a strong pasword. It's also important to enable multi-factor authentication if it is available for that particular account. For tips about enabling multi-factor authentication please read this and this article.
Conclusion
If you take these tips and best practices into account you can limit the risk of being phished. If you think you've been phished change your password for that particular service straight away and enable multi-factor authentication if you haven't done so yet.
That's it for today. More security tips tomorrow. In the meantime, stay safe online!




