With the blogs in this series I want to reach not only my typical audience, security professionals, but especially less security aware people to help them improve their personal security. If you think the content is helpful for people you know, share it with them!
Yesterday I explained why you should activate multi-factor authentication. In practice we're mostly talking about two-factor authentication (2FA). If you didn't read that post yet, please do so first.
Today I want to give you some more guidance on how to set up 2FA properly and how the choice of a good authenticator app on your smartphone can help you with that. Authenticator apps are a good middle ground between security and usability and when available they are the best option to use for the average user.
How authenticator apps work
Configuring 2FA with an authenticator app almost always works in a similar way for web applications and mobile apps. You have to scan a QR code on the application's website for which you're enabling 2FA. An entry for this website will be added to your authenticator app and you will get an activation code, which you need to enter on the website. Once 2FA is activated - depending on how the particular website implements it - you might be asked to enter a the token at a regular basis.
As a security measure the tokens generated by an authenticator app are only valid for a limited time, typically 30 seconds.
Should you rely on an authenticator app only and is any authenticator app good?
Sometimes you have to learn things the hard way. And that's exactly what happened to me. I got locked out of some accounts. Luckily for me I could regain access to them. But for a few accounts I needed to go through the account recovery process and I had to contact the particular companies to regain access to my account.
Regularly review your online account's #security settings! Just changed my authenticator app to Authy on a site where I still used Google authenticator. Reason? With Authy you can easily recover access when phone dies or is stolen. Trust me, I learned it the hard way 😆#Infosec
— John Opdenakker (@j_opdenakker) June 9, 2019
I used the Google Authenticator app and it worked just fine. And then once of a sudden my phone died. I got a new phone and at the moment I wanted to sign in to a particular website I was asked to provide a software token via the authenticator app.
And then my penny dropped.
I didn't have an authenticator app installed yet. But even after I did there was no way to generate the token to give me access to my account. To reconfigure 2FA you must have access to your account first. But Google Authenticator has no built-in backup and restore mechanism, so I wasn't able to recover the apps for which I had configured 2FA.
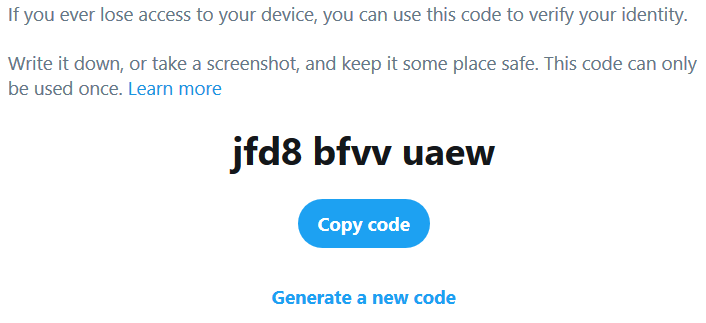
Luckily the number of accounts I couldn't access anymore was small. For most accounts I had recovery codes to regain access or I had SMS based 2FA enabled as a fallback option.
I learned a few lessons that I want to share with you, so you can prevent this from happening.
- Save backup codes when available! Do so securely in a password book or password manager. More info about secure storage of passwords can be found in this article.
- If backup codes are not available consider activating SMS based 2FA or security questions if they are available as fallback options. You can read some best practices about security questions here. Or better...
- Use an authenticator app with built-in backup and recovery functionality.
That's why I switched to Authy. When I changed phone recently restoring everything in Authy just worked like a charm.
I want to make a disclaimer here. I'm not incentivized by Authy to promote their authenticator app. I'm pleased with it, but any authenticator app that has backup and recovery functionality will do.
How to install Authy
This video shows how you can install Authy.
How to configure backup and restore and use Authy
Here and here you can find more about how Authy's backup and restore works and how you can use it to configure 2FA for an application.
Conclusion
Ask yourself for each user account for which you have 2FA enabled if you still would have access if your phone is stolen or breaks. Enable a fallback mechanism and use an authenticator app with backup and restore capabilities. More security tips tomorrow. In the meantime stay safe online!




