Public mailboxes are very handy. I use Mailinator regularly. But there are many, many more of them and they all work pretty much on the same premise. In this short write-up I will purely focus on Mailinator and show you the potential security risks. You can just create any @mailinator address you can come up with, go to the Mailinator website and open this mailbox.
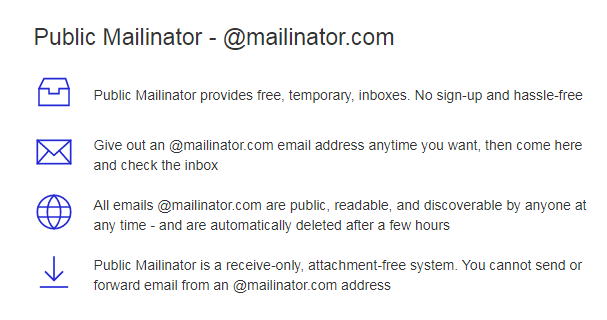
For instance if you open the mailbox [email protected] you'll see that several people already used it before, because it contains several spam mails.
Why would you use it
Mailinator addresses are perfect to use at account registration on websites where it's not necessary to provide your real personal data and therefore the Mailinator address can not be linked to you. One of the typical examples is an online newspaper where you need to register to read particular content. Use a mail address, like [email protected] and fake all other personal data at registration and you're good to go.
Mailinator and other public mailboxes are often used for testing because it's convenient that you don't have to create test email accounts. But if you don't think it through, this convenience might come at a serious price.
What are the security risks
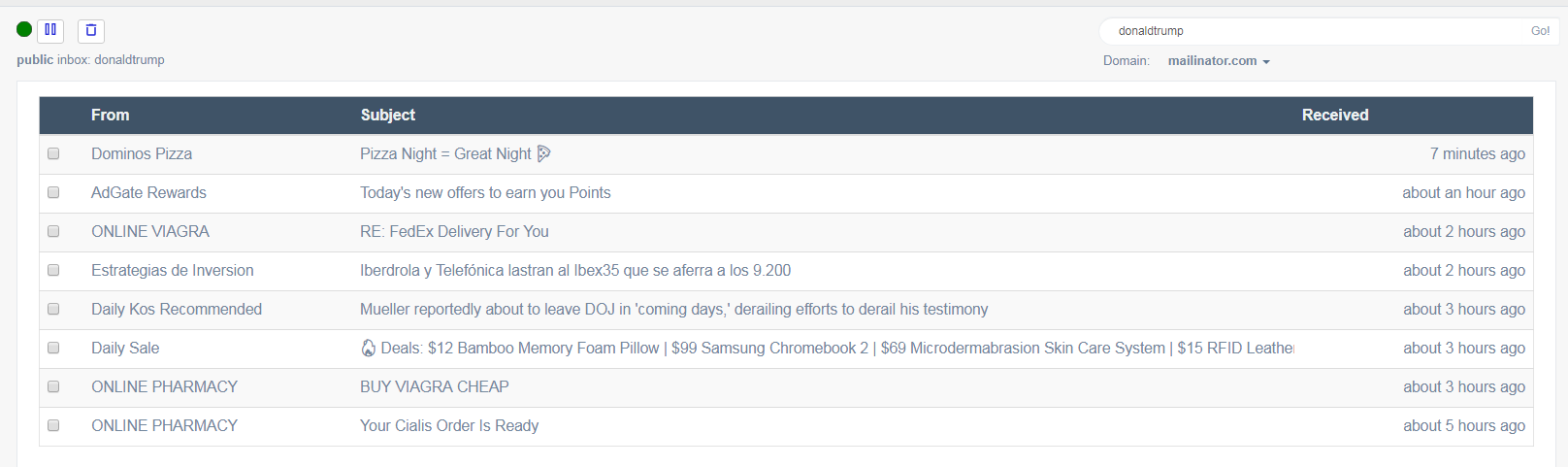
Like Mailinator describes, the free inboxes are public. This means that anyone that can guess the name of an inbox can see all the mails it contains. If someone opens [email protected] he can get access to the particular news website with the account corresponding with that email address. When it comes to reading news articles, I couldn't care less, but people also use it to register for other accounts. Some examples that I discovered in a few minutes time.
What we see here is a slack registration done with a Mailinator account. With this information I can perform an email reset, set a new password and get access to the particular Slack Channel in which confidential personal or company data might be exchanged.
Here's another one I found. Mail from Taco from Trello...
Again I have an email address that's used to register a Trello account that potentially contains data that can be abused by miscreants.
Or this mail containing a link to a hospital app to see a new notification.
I was curious to see if this was a phishing mail, but it wasn't classified as malicious by the various online virus/malware scanners I used. My best guess is that they used this very easy to guess Mailinator address to test some functionality.
The link leads to a login screen. Again because you know the email address you can perform a password reset and probably gain access to the system.
TL;DR
Only use public mailboxes when there's no risk to leak personal data or give unauthorized people a way to access accounts or other resources.
If you want to use it for QA testing purposes, use random Mailinator addresses, like this [email protected]. Given that this is quite hard to guess chances are really small that someone else will access the same mailbox. By the way, don't use this particular one anymore or I'll pwn you!
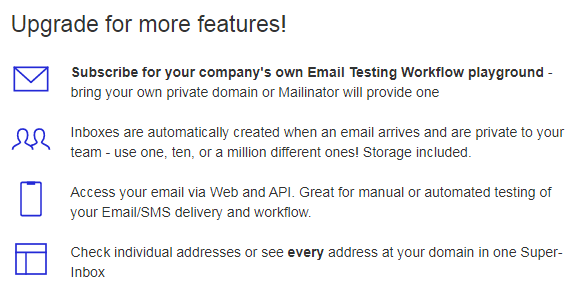
But the safest option is to use private mailboxes. Mailinator, and a lot of competitors have paid plans for it.