Today was the last day of SecAppDev. I had a bit of mixed feelings because it was a great conference, but I am also very tired after 5 intense days. I saw a lot of good talks, learned a lot and maybe even more important, met some awesome people. Kudos to Philippe De Ryck and Yo Peeters for the impeccable organization. If I have the opportunity I certainly go back next year.
That said, let me do a quick recap of the day. First on stage, Jim Manico with his talk “SSL / TLS / HTTPS best practices”.
Some impressions from another awesome @manicode talk at @SecAppDev 😂 pic.twitter.com/HJ7qjQZuzy
— John Opdenakker (@j_opdenakker) February 22, 2019
This was yet another entertaining and nicely built up session by Jim. It started with what TLS is about and a bit of history about the different SSL and TLS versions and their weaknesses. He showed a lot of real life examples to illustrate what can go wrong when you not configure TLS securely or when CAs are screwing up, to end with showing what a secure HTTPS is all about.
And I 100% agree with Jim that there’s no excuse anymore to not use HTTPS. Not doing is just negligent!
Next up was Seda Guerses. Her talk “Data protection by design” was all about how to translate the different GDPR requirements into actionable technical implementations.
Translating #GDPR into actionable system and software implementations is a pain in the ass. Some really good pointers in this excellent @SecAppDev talk by Seda Guerses. pic.twitter.com/563VloW56u
— John Opdenakker (@j_opdenakker) February 22, 2019
She shared several good insights on how to approach certain GDPR requirements and a lot of usable resources in this talk. Something certainly worth trying out is privacy threat modeling using the LINDDUN methodology
After lunch it was time for “Security features of TLS 1.3” by Cyprien De Saint Guilhem. Unlike the previous versions of TLS (1.0, 1.1 and 1.2) and even SSL2 and SSL3, TLS 1.3 is built from scratch. This implies that TLS 1.3 is much more secure by default.
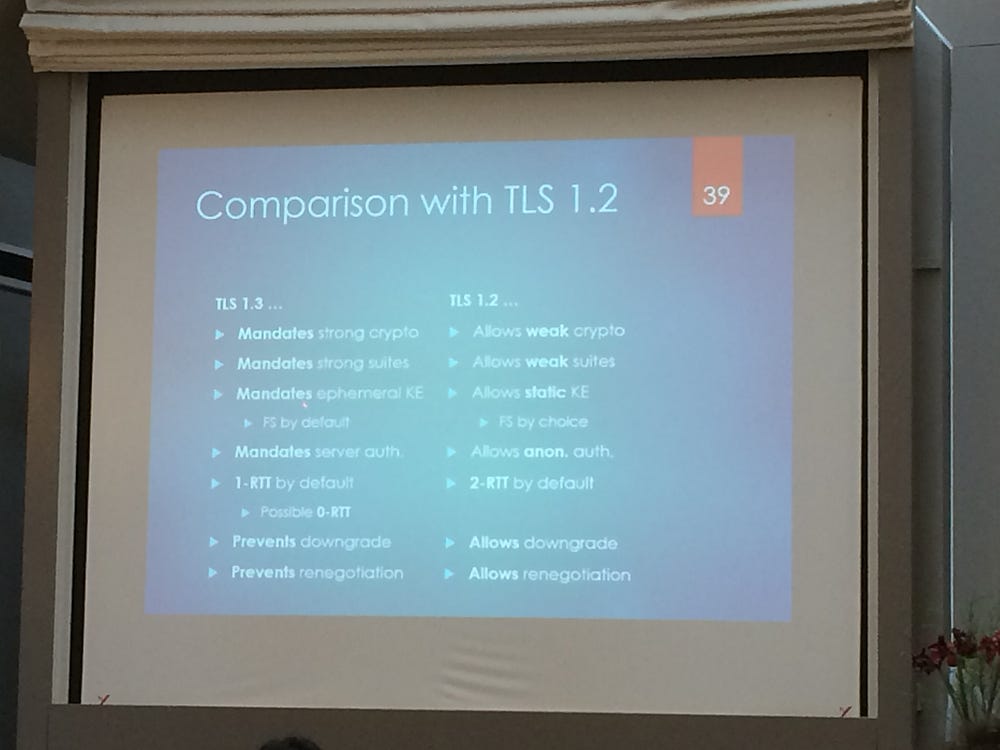
Very promising, but the adoption is still low (only around 10%) and not all major browsers support it yet.
Now it’s time for the last talk of @secappdev. @owasp ASVS by @manicode. pic.twitter.com/H82555eVoH
— John Opdenakker (@j_opdenakker) February 22, 2019
And then it was time again for Jim Manico. This talk was about the OWASP ASVS, which I have been using for a while now. ASVS stands for Application Security Verification Standard and is basically a list of secure coding requirements for developers and testers. It is divided in different levels, from 1 to 3. Depending on how critical your application is, it might need more rigorous security controls.
ASVS can be overwhelming at first, but you should fork it and adjust it to your specific needs. Start by rolling out the level 1 and guide the developers on how to implement these features, and even better let them decide on which features they are going to implement.
Some good practical tips for me on how to improve rolling it out. As a bonus we iterated through some of the ASVS requirements, made some modifications and pushed them to git.
Finally the conference was closed by Yo Peeters and Philippe De Ryck. For the interested the provisional date for next year is 09/03 - 13/03.
Read more about SecAppDev 2019 day 1, day 2, day 3 and day 4
